Notice: The usage of one private-public essential pairs is not supported in lots of wallets, as most wallets use BIP39 which permit a user to derive as many as two billion addresses for every supported copyright. Nonetheless, in the event you comprehend the hazards and ease/protection trade-offs, using a one private vital that controls just one address (in comparison to using a one mnemonic that controls and entire copyright vault), then it could have its place inside a portfolio of copyright property.
How can they be utilized by hackers to steal your cash? How can copyright rely on them to keep you safe? What can wallets do to maintain you Risk-free? What are you able to do to safeguard yourself?
And since copyright only displays the first and previous few figures, and You simply checked the primary and previous few characters, I had been ready to make you connect with another address that comes about to begin and conclude exactly the same way you anticipated.
But right before we dive into the small print let’s get you in control on what an Ethereum wallet is, and which one particular would match you the top.
Introducing G to by itself s occasions is similar to multiplying s * G. In actual fact, we can see this Procedure at a decrease level in by stripping absent several of the abstractions the library is providing.
One other crucial parameter in secp256k1 is definitely the starting point G. Due to the fact G is a degree around the elliptic curve, it can be 2-dimensional and has the parameters
The community interface and ttl parameters Permit the caller specify which network interface the take a look at will go through and the utmost number of hops the packets should really go through. A damaging value for that ttl will cause an IllegalArgumentException remaining thrown. The timeout worth, in milliseconds, suggests the maximum period of time the try must acquire. When the operation periods out prior to receiving a solution, the host is deemed unreachable. A damaging price will end in an IllegalArgumentException staying thrown.
Stack Trade network includes 183 Q&A communities like Stack Overflow, the biggest, most reliable on the net Group for builders to master, share their understanding, and Establish their careers. Visit Stack Exchange
When there is a protection supervisor, its checkConnect approach known as With all the local host name and -1 as its arguments to see Open Website When the operation is allowed. In the event the operation is just not permitted, an InetAddress symbolizing the loopback address is returned.
At this moment it is actually making use of several (based exactly how much cores it detects) employees on CPU, but probably it is achievable to also apply mining it on GPU applying
Notice: This tends to generate a 32 bytes sequence. It in no way verifies which the sequence is a valid private vital.
Most copyright consumers tend not to double-Verify what the Dapp and (or) browser wallet are exhibiting. They don’t hassle to examine if the wallet transaction is exhibiting the exact same point as the things they are expecting. The word “precisely�?is stressed.
Be cautious using the designed-in random number library for Python. It’s not intended to be cryptographically protected. We propose familiarizing yourself with cryptographically safe randomness if you are new to The subject.
Most wallets also give you a mystery recovery phrase, an important backup for accessing your funds in case of system decline. With most of these Ethereum wallets, you can develop various accounts and restore them all with The key Restoration phrase.
 Mara Wilson Then & Now!
Mara Wilson Then & Now! Judd Nelson Then & Now!
Judd Nelson Then & Now!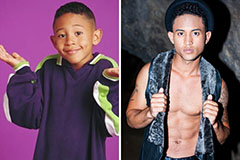 Tahj Mowry Then & Now!
Tahj Mowry Then & Now! Brandy Then & Now!
Brandy Then & Now! Nicki Minaj Then & Now!
Nicki Minaj Then & Now!